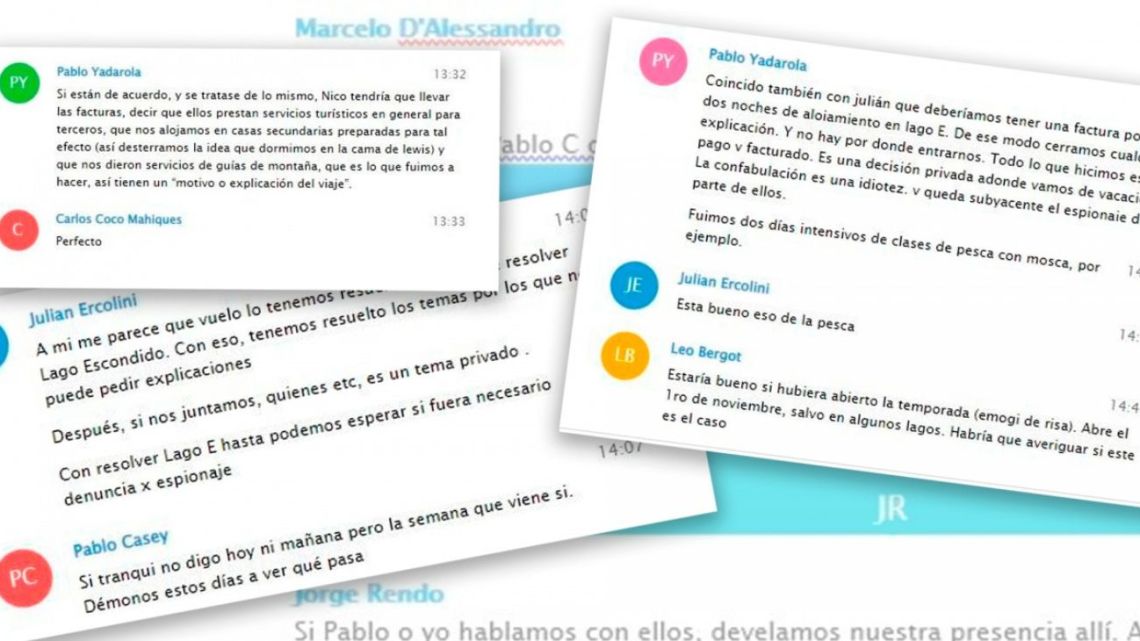
The filtering of private conversations between federal judges, Buenos Aires officials and media entrepreneurs, who sought to hide the invitation from Grupo Clarín and the tycoon with false invoices joseph lewis to his mansion in Barilochense hidden lake, raises more questions than answers. One of the most pressing – beyond why the protagonists established their collusion with texts and audios – is how it happened. In the last hours she managed to show the first clues.
Journalist horace verbitski surely the chats “are part of a filtration made by hackers in the place https://violado.vc/ [la extensión de dominio correspondiente a la nación caribeña de San Vicente y las Granadinas], which ask for 600 dollars to be paid in bitcoin or Monero cryptocurrencies, for 500 MB of information. The hacking was carried out on the telephone of the Minister of Security of the Autonomous City of Buenos Aires, Marcelo D’Alessandro”, one of the guests to the south.
Santiago Rey: “They request the arrest in Bariloche of Marcelo D’Alessandro and the administrator of the Joe Lewis ranch”
The robbery technique would have been the sim swapping: access to a person’s phone chip by posing as them. “The company is requested a new chip reporting a cell phone theft. The company sends it without a complete check of the applicant’s identity -they hardly ask for the DNI- and with that it is possible to access the entire file, when entering the sessions opened by the victim,” the newspaper explained. Argentinian time. “That’s when the duplicate chip takes control of the line and with it all the personal data is extracted.”
This year the Minister of Health of the Province of Buenos Aires, Nicholas Kreplak; the former Minister of National Security, Sabina Federico; the national deputy of the left front, Myriam Bregmann; and his colleague from the Frente de Todos, mara brawer.
Juan Manuel Valdés: “We need an agreement on the policy of not using espionage against the adversary”
On the other hand, a Telegram account (the application of Russian origin used by travelers) can hack scam programs such as Pegasus, the application of the Israeli company NSO that is installed on the phone through some link and starts working in the background to read messages, listen to calls, access photos and even locate the user via GPS. The vulnerability can be increased when using Telegram Web, which allows using the messaging system from the computer. If the session remains open, the exposure becomes greater, since there are programs developed specifically for those situations.
Although they do not reduce the guarantee of 100% protection, some options provided by Telegram itself allow you to increase the chances of hack. Among them is the restriction of users who can see the phone number or make calls to the owner, the inclusion of a lock code each time they want to use the application and -perhaps what would have been advisable for those involved in the case hidden lake– The “secret chat” option so that messages are not saved in the cloud and self-destruct in a reasonable amount of time.
JL
You may also like